Problem with certificate and loginscripts
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-11-2016 01:21 PM
Many computers are failing loginscripts periodically -- like 80% of the time they wont work. the other 20%, they're fine. These scripts worked fine for the first 6 months we were using them. Only recently having an issue (maybe related to an update we did last month?)
I've re-enrolled the computers, and they download certs, and everything enrolls properly.
This only affects login scripts -- log out scripts are working fine.
I've re-created the policys that apply the script, and done some blank pushes.
This is what the jamf.log shows:
Thu Feb 11 11:56:17 dmlmac8 jamf[4295]: Checking for policies triggered by "login" for user "username"...
Thu Feb 11 11:56:19 dmlmac8 jamf[4295]:
There was an error.
The jamf binary could not connect to the JSS because the web certificate is not trusted.
On the same computer when i test the jssconnection, I get this:
$ /usr/local/bin/jamf checkJSSConnection
Checking availability of https://jss.*:8443/...
The JSS is available.
so it can connect to the jss regularly, just not during the login event? what am I missing?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-11-2016 03:34 PM
oh look, heres one that had the problem, then an hour later for the next user -- didnt have the problem. so strange:
The jamf binary could not connect to the JSS because the web certificate is not trusted.
Thu Feb 11 12:53:50 dmlmac12 jamf[234]: Informing the JSS about login for user abc
Thu Feb 11 12:56:43 dmlmac12 jamf[60172]: Checking for policies triggered by "logout" for user "abc"...
Thu Feb 11 12:56:45 dmlmac12 jamf[60172]: Executing Policy University Libraries: Logout - DML Script
Thu Feb 11 12:59:05 dmlmac12 jamf[60526]: Informing the JSS about login for user cba
Thu Feb 11 12:59:06 dmlmac12 jamf[60526]: Checking for policies triggered by "login" for user "cba"...
Thu Feb 11 12:59:07 dmlmac12 jamf[60526]: Executing Policy University Libraries: Login - DML Script
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-11-2016 07:19 PM
I'd be looking into this
The jamf binary could not connect to the JSS because the web certificate is not trusted- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-12-2016 10:18 AM
@calumhunter Yeah, definitely a cert issue...however, that cert issue only applies sometimes. Sometimes it doesnt connect -- therefor the login doesnt run. but sometimes it does connect. any idea why it might be so intermittent?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-13-2016 12:15 AM
@Krytos Can you give some details of the setup?
Self signed cert? Behind a load balancer?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-16-2016 09:52 AM
@bentoms Yes we're using the jss self signed cert. No load balancers are affecting either the JSS server or any of its clients.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-17-2016 04:21 AM
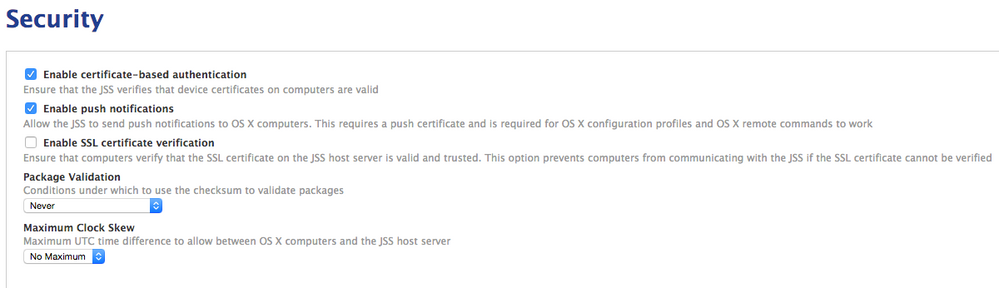
@Krytos Is "Enable SSL certificate verification" checked under Computer Managment > Security ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-17-2016 09:00 AM
@bentoms No, that check box is unchecked.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-22-2016 09:03 AM
still having issues with this. any ideas?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-22-2016 09:15 AM
I am having the same issue. Mine is much more intermittent. Start up policies, logout policies, and check in policies all run fine. It is just the login policies that give the error. I have contacted tech support but they don't have any clue what it causing it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-01-2016 04:49 PM
I'm seeing the same thing here. Let me know if you have any ideas/suggestions. If i find anything or have any updates, I'll be sure to share.
Thanks.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 06-27-2016 08:38 AM
Yep im getting the same, did anyone get a fix for this?
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 07-28-2016 06:41 AM
We are experiencing this as well, seems to only affect login policies as previously mentioned. Enable SSL verification is unchecked also.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 08-15-2016 02:59 PM
We are having the same issue here, only on login policies. We just bought JAMF a few weeks ago to manage a few hundred macs across a school district. I've been working every day on policies and scripts to get these computers working with their network homes and shared drives. School starts next week and login policies are pretty much broken one out of every 4 logins.
My JAMF rep said its a known issue and they are "working on it". The only work around they can give me is to replace all my login policies with launch daemons. I don't have time to rework my whole process... This is going to be a very bad start to the year. I thought this product was enterprise ready, this seems like a big issue that hasn't been resolved for MONTHS.
For now i'm going to tell the teachers if their mapped drives don't show up to logout and log back in again. They will be pretty upset about the extra work...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 08-20-2016 03:38 PM
@TexasITAdmin Maybe try this?, this way it's using a LaunchAgent.
Also, is your JSS's SSL signed by an internal CA?
(ccing @daz_wallace )
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 08-21-2016 12:06 AM
Hey all,
Like @bentoms, I'm a consultant for an Mac MSP. Randomly we had this same issue on one customer's brand new JSS install and had to switch to Launch Agents as a fix due to time constraints.
I was told its a known highly intermittent issue since 9.82 and was asked to login, and logout ten times and send a copy of the system log and JAMF log from an affected Mac. Sod's law I couldn't get it to fault to be able to send helpful information to support.
My suggested tests / workarounds would be:
- get a signed cert and retest (could get a free short term one from Let's Encrypt)
- disable (temporarily) the two options in Keychain Utiltiy for checking cert validity (I think one is called CRLP, but it's in the application preferences - sorry no access to a Mac this weekend)
- a last idea, as this only seems to affect the login trigger, is to create your own LaunchAgent that just runs 'JAMF policy -event trigger [add username option]' and see if that helps (that command is incomplete and you'd need to check your 'JAMF -help' page for the specific commands)
At the end of the day, it looked like, for some reason that the client was ignoring the custom 'trusted' settings for the SSL cert. I'm not sure if this was the OS, the JAMF binary, or the command the JAMF binary uses.
Good luck, and keep working with your JAMF support guy to crack it.
Darren
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 03-07-2017 01:52 PM
Any update on this from Jamf?!?! We have been getting many reports lately from students/staff and we are thinking about turning off all of our policies that rely on Login/Logout hooks because of it's lack of reliability. We currently do our drive mapping via login scripts for our domain users. Our temporary solution has been creating a Self Service policy to allow users to map the drives if the login script failed to run. On a campus of around 150 machines, this has been happening multiple times every day. We'd hate to convert everything to launch daemons just to have the issue fixed in an upcoming JSS upgrade.
Thanks!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 03-15-2017 08:36 AM
@bmccune No updates. I created a ticket with support about this. I suggest you do the same so they know we are still having issues with this. Their reply to me was an unhelpful "This product issue is still open and we do not have any status updates at this time. Please feel free to keep an eye on release notes in future versions of the JSS to see if this has been addressed."
They still push using launch daemons to trigger login policy. However, when you manually invoke login policy its LDAP blind and anything you had assigned to LDAP groupings (like mapped drives!) gets skipped.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 03-15-2017 08:53 AM
Also @bmccune upvote the following two feature requests as those if implemented will resolve the issues cause by their LaunchDaemon work around.
Also, being able to scope policies via LDAP in general is really useful for school environments especially when different classes have different software/login needs.
https://www.jamf.com/jamf-nation/feature-requests/4841/ldap-group-policy-limitations-for-all-triggers
https://www.jamf.com/jamf-nation/feature-requests/4340/allow-scoping-policies-to-specific-users-based-on-ldap-membership