We have deployed Pulse Secure 9.1.9 into production and my macOS 10.15.x Catalina Macs are now prompting users to...
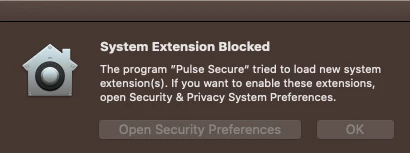
1 Approve the System Extension in System Prefs Security & Privacy Pane (this pop-up is similar to older Kernel Extensions).
2 Approve "Filter Network Content" (this is a new pop-up warning).
These warnings tend to scare my users and the users usually click the wrong buttons (or ignore the messages).
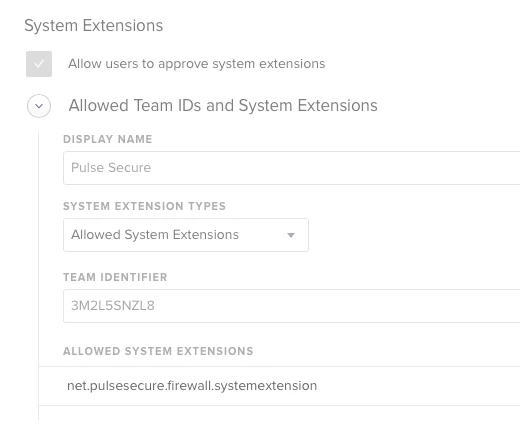
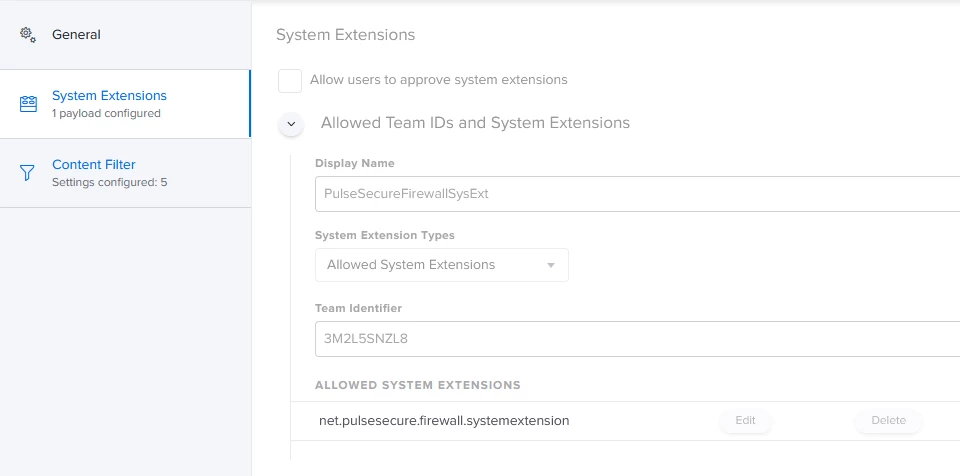
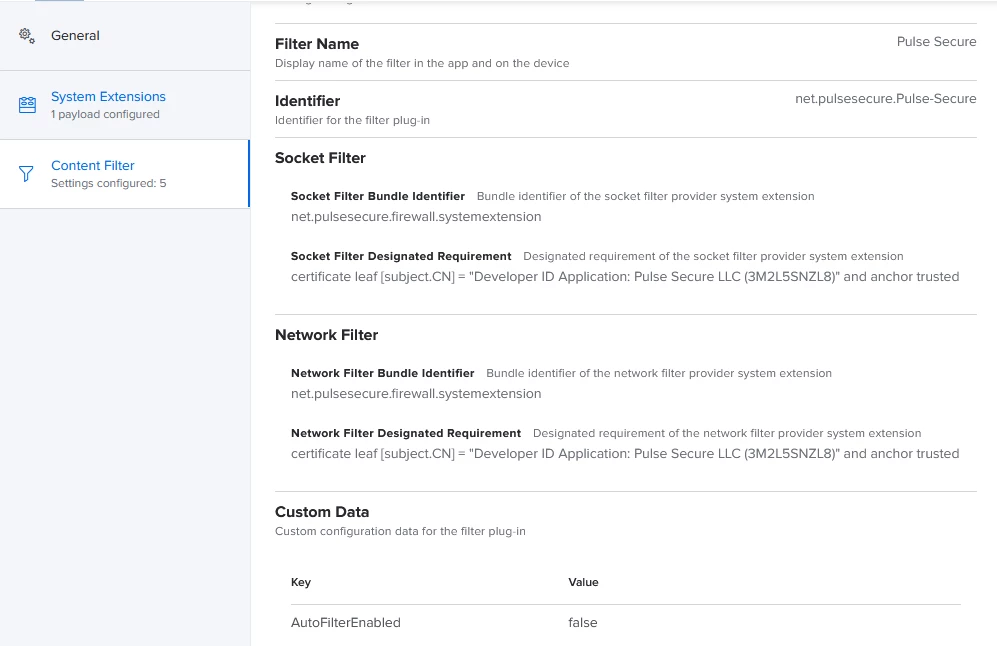
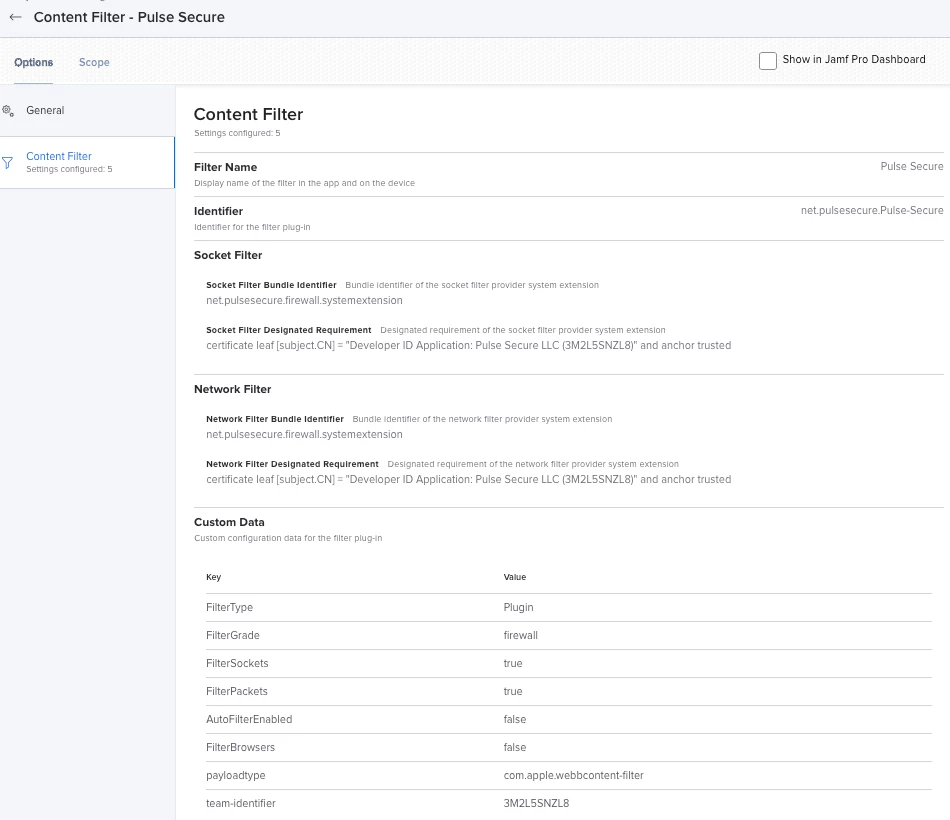
To proactively mitigate this issue, I have created a Jamf MDM profile with a System Extension Approval payload. However, my Catalina users are still getting the pop-up warnings when Pulse Secure 9.1.9 is launched for the first time. I assume the same issue will apply for Big Sur too (Which I don't have in production yet but I see similar behavior in my test environment).
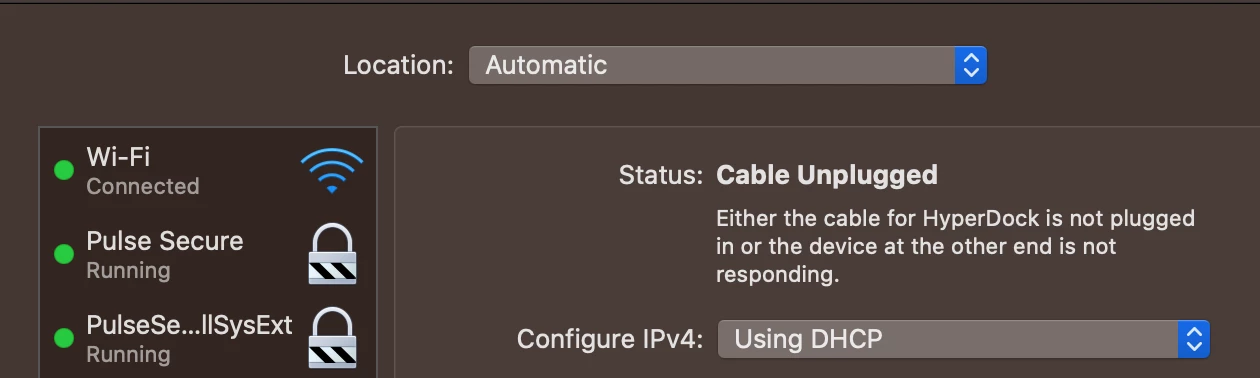
In some cases, the System Extension appears to be approved, but the second "Filter Network Content" warning is not approved.
I have read all the applicable Pulse Secure support KBs on this matter. I think I'm doing this correctly.
Is anyone else wrestling with this issue in Catalina (or Big Sur)?
(See attached screenshots).