- Jamf Nation Community
- Products
- Jamf Pro
- Re: FileVault 2 - Reissue Key on High Sierra Escro...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
FileVault 2 - Reissue Key on High Sierra Escrow Problem
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 08-07-2018 07:39 AM
I've used the script available via JAMF support on GitHub to issue a new personal FV2 key to an already FV2 encrypted computer running High Sierra. (https://github.com/JAMFSupport/FileVault2_Scripts/blob/master/reissueKey.sh)
The script successfully changes the personal key, but the new key does not escrow on the JAMF server.
I've tested this by using the script to change the key and then attempted to use the previously escrowed key to access the computer. The old key fails.
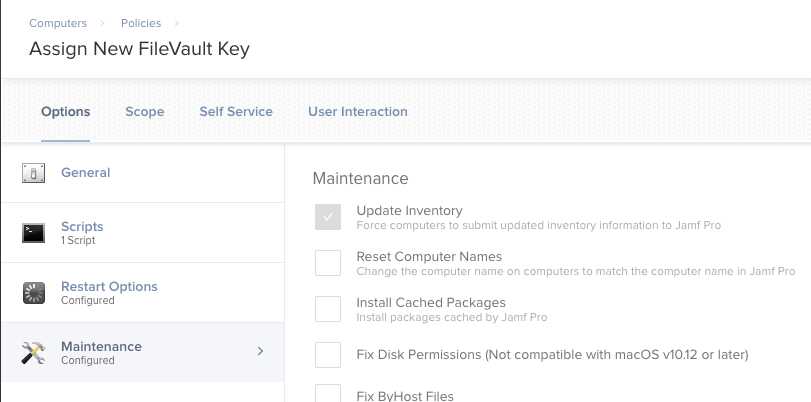
I have a config profile in place which I thought would get the new key onto the JSS (see the screen shot).
Has anyone successfully accomplished this on High Sierra? Any input would be greatly appreciated.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 08-07-2018 08:19 AM
I've found that with high sierra, the key does not get sent to Jamf until an inventory update occurs. On one of your machines that has the new key, go to terminal and type
sudo jamf reconand see if they key is in Jamf after that.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 08-07-2018 08:46 AM
@bmortens115 Thank you for the response.
I've included an inventory update in my script (see attachment), and manually completed a "sudo jamf recon" at least 4 times.
Unfortunately, the key on the JSS is still not updating.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 08-08-2018 07:51 AM
hmm has the config profile ever been removed after you sent it out? I would check the config profiles logs and see if anything weird was changed and check the logs of the computer for anything out of place (/var/log/jamf.log)
I have never had an issue with the FV2 Key escrow on a 10.13 machine, unless the config profile was removed from the device
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 08-08-2018 09:10 AM
@Mr.Einstein , I've used this script at my previous job and it worked except for in one case. Somehow, after upgrading to 10.13, the user did not get a secure token. This was the only account on the laptop and it was a bit of a mystery how it didn't get a secure token. To check, use terminal to run sysadminctl -secureTokenStatus username
It will either say Enabled or Disabled for the user. Hopefully, yours is enabled.
Good luck!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 08-08-2018 11:07 AM
@Mr.Einstein You may be encountering PI-005560:
[PI-005560] When a new FileVault key is escrowed, FileVault individual recovery keys report as invalid or unknown for computers with macOS 10.13.x. Workaround: Reboot the device, and submit an inventory update.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 08-10-2018 11:59 AM
@bmortens115 @dan.snelson @jriv
Thanks for the tips everyone.
@bmortens115 I knew "bmortens" sounded familiar. You were actually the one who did our initial on-site JAMF setup/training a couple of years ago. It's nice to see you around the forum.
Unfortunately, I was unable to get this particular MacBook to escrow the new FV2 key, but fortunately this was just on a test Mac.
I went ahead and tried it on two production machines for more testing, and the script > recon > escrow process worked flawlessly.
I'm ready to get the new keys rolled out to the necessary computers.