- Jamf Nation Community
- Products
- Jamf Pro
- Re: How To Kernel Extension in High Sierra
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
How To Kernel Extension in High Sierra
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 10-04-2018 09:25 AM
How To Kernel Extension in High Sierra
Couldn't find an All in One Place regarding Kernel Extension information so here we go. Creating this thread so everyone can Chip In Best Practices. - Link to a thread like this if im wrong about not having a thread like this so we arent redundant
Kernel Extension List - https://docs.google.com/spreadsheets/d/1IWrbE8xiau4rU2mtXYji9vSPWDqb56luh0OhD5XS0AM/edit#gid=8111306...
via gui you can do the following
I believe 10.13 & up you can locate them at /Library/StagedExtensions/Library/Extensions
You can then find the BundleID by right clicking the kernel extension you want & select show package contents, then in contents directory you can open the .plist and view
for Team ID I only know this way - https://technology.siprep.org/getting-the-team-id-of-kernel-extensions-in-macos-10-13-and-higher/
In terminal run
sqlite3 /var/db/SystemPolicyConfiguration/KextPolicythen once in db run following command
SELECT * FROM kext_policy;it will produce the Team ID & associated KEXTS
What are methods / best practices you use?
Looking for a Jamf Managed Service Provider? Look no further than Rocketman
________________
Virtual MacAdmins Monthly Meetup - First Friday, Every Month
- Labels:
-
Configuration
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 10-16-2018 05:38 PM
I've used this before, but lately when I run the commands above the sqlite results come back blank, any ideas? This happens on multiple machines, whereas a couple of weeks ago it wasn't a problem..
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 10-17-2018 02:47 AM
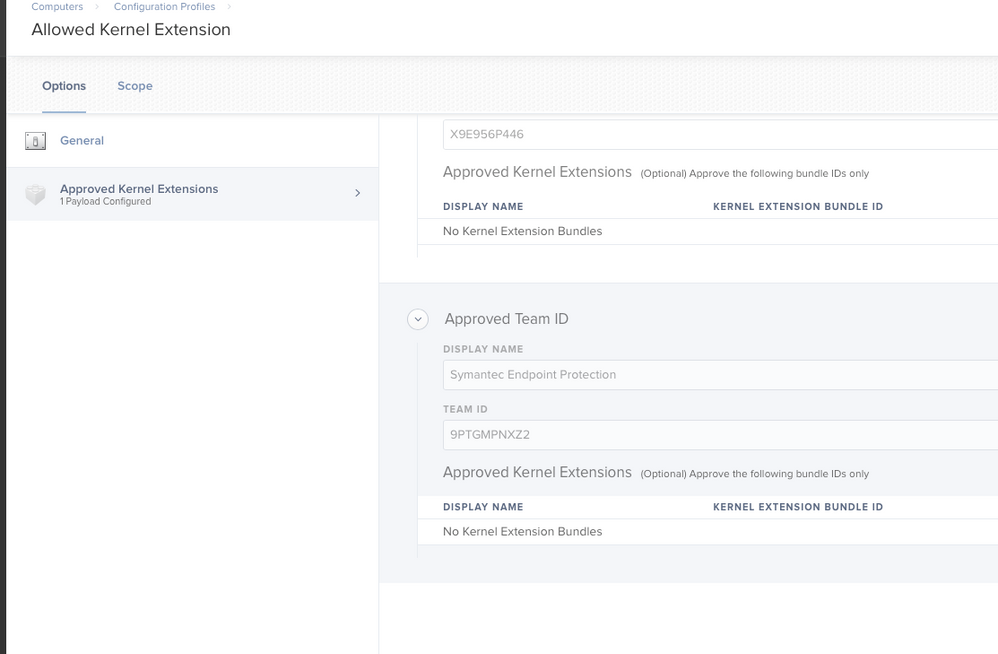
I was looking into this earlier in the year! JSS version 10.6 allows you to deploy a config profile for Kernel extensions. Once you create it and scope if a new Kernel Extention is needed just update already deployed one and it will update all your endpoint.
I'm using this CP for deploying KEXT for SEP 14.2 , Pulse Secure 9.0.2 and NextGen AV
hope this helps
RK
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 10-17-2018 08:57 AM
@rkelegha We are on 10.7.1 and have been trying to deploy a couple of KEXT to 10.13.6 machines. The profile gets installed but the extension is never allowed. I entered the right TEAM ID but it just doesn't do what it's supposed to. Do you have any special trick ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 10-17-2018 02:07 PM
@cyepiz thats very strange, could you share some screenshots of your results, are these kexts deployed via JAMF?
if you install a kernel extension locally to a machine, does it show then?
Looking for a Jamf Managed Service Provider? Look no further than Rocketman
________________
Virtual MacAdmins Monthly Meetup - First Friday, Every Month
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 10-23-2018 12:39 PM
Please see the attached image ...
Open JSS
Click on Computers
Click on Config profiles
Click "new"
Very last config profile is Allowed Kernel extension
Leave it up to you to play around :)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 10-23-2018 12:39 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 10-23-2018 01:30 PM
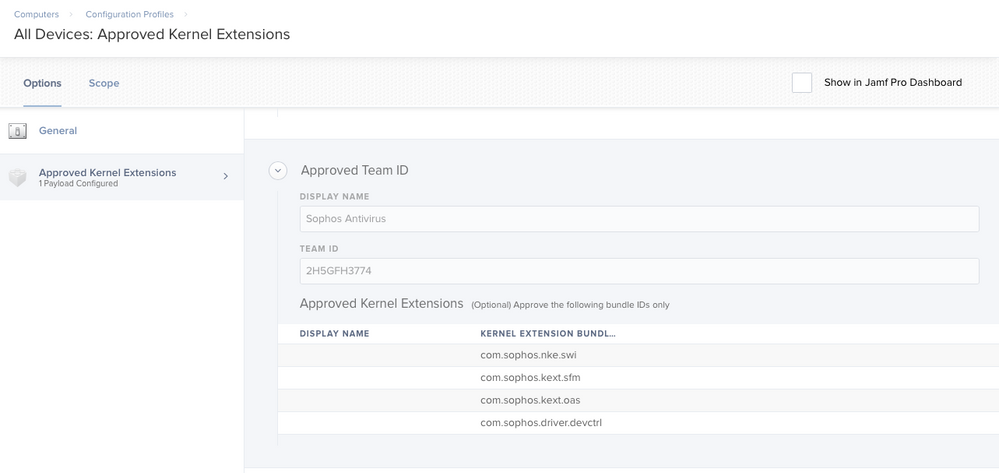
@rkelegha Try adding the Bundle ID's listed in the Google Sheet to your Symantec KEXT. Attached is a screenshot of our Approved KEXT's Profile.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 10-24-2018 01:08 PM
Remove the bundle ID's they are not needed.. just the TEAM ID should do..
rk
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 10-24-2018 02:00 PM
You can also run this command to get the team ID of an application. I've had to use it for GlobalProtect VPN.
codesign -dv --verbose=4 /Applications/YourApp.app- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 10-31-2018 04:05 PM
@rkelegha & @JoshRouthier -- Any reason why or why not to leave out the Bundled ID's?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 11-01-2018 02:44 AM
- There a not needed as the TEAM ID will cover all bundles for KEXT 2 . I didnt and it worked for me :)
rk
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-05-2019 04:44 PM
Has anyone encountered an issue where they unchecked the "Allow users to approve kernel extensions" and now the option to "Allow" in Security & Privacy no longer appears. I have rechecked the box and pushed it back out but even after restarting I am unable to get the "Allow" to show.
The only fix I have found so far, is to touch every machine and reboot into recovery, go to terminal, and enter "spctl kext-consent disable"
Background: I was trying to make it to where Sophos didn't require the user to click "Allow" after installation. Added the team ID alone didn't fix at first, I disabled the "Allow users to approve kernel extensions" and it stopped appearing. I then ran into the issue on other machines a day or so later where the "Allow" option wouldn't appear at all for software that we didn't already have approved extensions established for.
Any assistance would be great.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 03-11-2019 12:52 PM
So has anybody seen teh Kernel extentions not working after an in place upgrade from 10.13.3 to 10.14.3?
The Config Profile says Completed before I start the upgrade.
I was also thinking maybe because 10.13.3 doesn't know about Kernel Extensions, so then how do you make the timing work?
ANy ideas?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 03-11-2019 01:51 PM
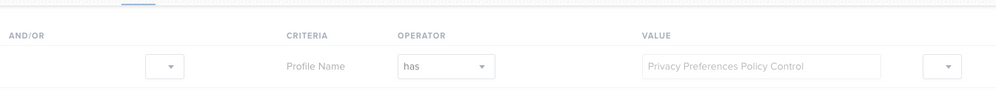
@szultzie The kext profile was live in 10.13.4, so that makes sense that you're seeing that issue if the profile is being installed while the user is still on 10.13.3.
If you're using the Jamf-supplied PPPC profile that automatically installs after a user logs into Mojave for the first time post-upgrade, just make a smart group and scope your Kext profile to the presence of the PPPC profile. That should make sure the profile gets there quickly.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 03-11-2019 02:16 PM
@szultzie Profiles generally only apply their magic once. 10.13.3 didn't know anything about UAKELs so when you pushed the profile to those machines it ignored it. As such, the profile won't magically wake up when you update/upgrade to 10.13.4+. Same with PPPC in 10.14.0+
What we do is scope UAKEL whitelist profiles only to machines ≥10.13.4. PPPC profiles scoped only to ≥10.14.0. The idea is you don't want to push a profile to a machine that doesn't know what to do with it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 03-27-2019 11:52 AM
When trying to send kernel extension payload I get this as the error, any suggestions?
"The profile's payload did not validate properly."
Currently running 10.14.3
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-19-2019 07:21 AM
@achristoforatos "The profile's payload did not validate properly."
have you manually verified the bundle id & team id for the specific application of the kernel extension ?
Looking for a Jamf Managed Service Provider? Look no further than Rocketman
________________
Virtual MacAdmins Monthly Meetup - First Friday, Every Month
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-24-2019 01:22 PM
@Hugonaut Thanks for the response. Turns out I had a lower case J. That was the issue. Case sensitive. Thanks for the help.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 07-16-2019 09:08 AM
Does the sucessful use of this profile done thru Jamf's built in Kernel Extension whitelist mean that the pop up does not show? Or does it mean that the pop up does show but that the user can allow without unlocking the Security tab in System Preferences? I'm testing this with McAfee on 10.13.6 using only the TeamIdentifier GT8P3H7SPW. The pop up still shows when in install McAfee 10.6.2 on a system but users can hit allow. Is this right? Should the pop show or not show at all?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 08-07-2019 08:37 PM
Hi @Hugonaut
The sqlite command you are using its second column values give you the Bundle Id of the software, why double the work. Use the following command on the sqlite prompt to find out the fields of the 'kext_policy' table.
PRAGMA table_info(kext_policy);
The following lines are copied from my computer.
sqlite> SELECT * from kext_policy;
9PTGMPNXZ2|com.symantec.ips.kext|1|Symantec|5
9PTGMPNXZ2|com.symantec.internetSecurity.kext|1|Symantec|5
9PTGMPNXZ2|com.symantec.nfm.kext|1|Symantec|5
TXAEAV5RN4|com.epson.driver.EPSONProjectorAudio|1|EPSON|1
TXAEAV5RN4|com.epson.driver.EPSONProjectorMPPAudio|1|Seiko Epson Corporation|1
9PTGMPNXZ2|com.symantec.SymXIPS|1|Symantec|1
sqlite> PRAGMA table_info(kext_policy);
0|team_id|TEXT|0||1
1|bundle_id|TEXT|0||2
2|allowed|BOOLEAN|0||0
3|developer_name|TEXT|0||0
4|flags|INTEGER|0||0
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 08-07-2019 10:23 PM
I would also like to know the answer to that @Kyuubi.
We are looking at moving to Sophos Central and I'd really rather avoid the hassle of having our 950+ users click 'Allow'.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 08-08-2019 05:05 AM
@Kyuubi If the kext has been approved correctly there won't be a notification at all.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 10-02-2019 12:19 PM
@trlatimer Did you ever find another method of resolving this problem ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 11-08-2019 11:21 AM
@trlatimer I'm also curious if there was a resolution to this issue?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 01-23-2020 08:48 AM
anybody getting the "blocked system extention" when they upgrade to catalina?
Im getting it now :(