- Jamf Nation Community
- Products
- Jamf Pro
- Re: Download Security Update 2021-001 for Catalina
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Download Security Update 2021-001 for Catalina
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on
02-04-2021
02:49 PM
- last edited on
03-04-2025
08:52 AM
by
![]() kh-richa_mig
kh-richa_mig
Does anyone have URL to download Security Update 2021-001 for macOS 10.15 Catalina?
Is so, would you share, please? Thanks!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-09-2021 12:09 PM
@mhasman Just published - https://support.apple.com/kb/DL2068 - for Catalina 2021-001... but nothing yet for Mojave 2021-001. :-(
Tempting me to put Boot Camp on my Intel Macs and get actual timely OS updates and patches from a real OS vendor who understands supporting technologies from more than 2 years ago. :-p
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-09-2021 12:11 PM
Be aware that Security Update 2021-001 Catalina does not include the fix for CVE-2021-3156 (sudo vulnerability). For that you'll need macOS Catalina 10.15.7 Supplemental Update 10.15.7 which is not yet available to download from support.apple.com (it is however available to install via Software Update)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-09-2021 05:45 PM
Question now is where to download Supplemental Update 10.15.7 02/09/2021 :)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-09-2021 07:43 PM
Or more to the point, how long will it take Apple to release the standalone .pkg installer for it? It was 8 days from Security Update 2021-001 Catalina being released via Software Update and the .pkg becoming available from support.apple.com. Let's hope Apple beats that time with the macOS Catalina 10.15.7 Supplemental Update 10.15.7 .pkg.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-10-2021 06:26 AM
@sdagley I'd like to think the prolific complaining I have been doing in the past week has helped - they're all posted as downloads now... but not well-named, and ever since Security Update 2020-006 for Mojave I think Apple owes it to us to at least state on the download page whether the update is cumulative or requires the preceding version be installed.
For example, what's the difference between:
https://support.apple.com/kb/DL2068 - Security Update 2021-001 (Catalina)
https://support.apple.com/kb/DL2071 - Security Update 2021-001 (Catalina)
A few minutes ago those pages were identical although except for the download links; while the text of the latter has been updated to read "macOS Catalina 10.15.7 supplemental update" but the header still says Security Update 2021-001 (Catalina)
You would think with the marketing budget Apple has they could pay someone enough to ensure consistency in release naming... they're not winning any bonus points from me:
Big Sur = minor point release
Catalina = supplemental update
Mojave = security update
Speaking of Mojave here's the latest:
https://support.apple.com/kb/DL2070 - Security Update 2021-002 for Mojave
And for those who - I can't anticipate why - might really need it:
https://support.apple.com/kb/DL2069 - Security Update 2021-001 for Mojave
A penultimate complaint - this naming scheme (or lack thereof) is really going to muddy the waters when the NEXT security updates are released... presumably we'll be looking at 2021-003 for Mojave, 2021-002 for Catalina, and Big Sur 11.2.2 or 11.3.1 depending on how far Apple's progressed with features before zero days require them to patch again. leading me to...
One final complaint - https://support.apple.com/en-us/HT212177 defining the security content says it fixes the sudo vulnerability - CVE-2021-3156 - as well as a couple Intel graphics drivers. Do we really need to download 1.7GB+ to each Mac needing updates for a 500k binary (sudo) plus generously 500MB for the graphics drivers? How I miss the old days of incremental updaters and combo updaters... if your fleet's well maintained you should only need to push the 500k to fix sudo!
Oh, to end on a useful note, in my correspondence with Apple where I was complaining about the lack of standalone downloads from the support site, I was advised that, for limited testing on isolated systems that couldn't run software update, one could always download the associated assets from the same catalog ID along with the .dist file, and with them all in the same folder, run:
/usr/sbin/installer -target / -pkg /path/to/folder/with/pkgs.distI had no idea you could do that with the .dist files, I always wondered what purpose they served! Mind you this is for TESTING and specifically NOT RECOMMENDED for deployment to your fleet... but it's another tool in my belt.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-10-2021 08:25 AM
@gabester Thanks for sharing that .dist trick, but after looking at today's version of Security Update 2021-001 with a post date of 2021-02-08 (https://support.apple.com/kb/DL2071?viewlocale=en_US&locale=en_US) as opposed to the version made available yesterday with a post date of 2021-02-05 (https://support.apple.com/kb/DL2068?viewlocale=en_US&locale=en_US) it appears that Apple is re-writing history by re-releasing macOS Catalina 10.15.7 Supplemental Update 10.15.7 as Security Update 2021-001 (Catalina)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-10-2021 09:26 AM
@sdagley according to my NetSUS, they re-released "macOS Catalina Security Update 2021-001" (19H524) and there's the "macOS Catalina 10.15.7 Supplemental Update" maybe is the latter for those Macs with the first release of "Security Update 2021-001" installed (19H512) ???
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-10-2021 10:04 AM
@carlo.anselmi Probably as users seeing Security Update 2021-001 (Catalina) re-appear after it was installed would be a definite cause of confusion.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-11-2021 02:03 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-16-2021 08:35 AM
Is there a direct link anywhere to the actual February 9th release (only available in Software Update)? Everything I can find is the "older" 20201-001 released on 2-8-2021.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-16-2021 09:37 AM
@tomt https://support.apple.com/kb/DL2071 is the URL to download the DMG containing the standalone pkg, which is effectively a combo updater for Catalina 10.15.7 to build 19H524. You don't need to install the previous same-named Security Update 2021-001 to build 19H512 first.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-16-2021 01:01 PM
@gabester So I downloaded the file you linked to and attempted to install it on a 2018 MBP with OS build 19H15. Install failed.
I think I'm slowly losing my mind. Time to wipe this box and start again. Just in case it is something on this particular machine. I do appreciate the help so far.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-16-2021 01:11 PM
@tomt Any chance that Mac is subject to SSL inspection on traffic to external sites? One thing that .pkg doesn't contain is the bridgeOS update for Build 16H524. That has to be downloaded from Apple's servers, and will fail if SSL inspection is used.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-16-2021 01:21 PM
@sdagley That's a good thought. While it's possible our messed up network could be doing inspection, I've had Apple's CDNs added to our bypass list for a while now. I'm thinking you are onto something with the bridgeOS update being a prerequisite.
I miss the days of simple Combo updates...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-16-2021 01:34 PM
@tomt It's an ongoing battle :-). Note that Apple did update the Use Apple products on enterprise networks KB article in December, and there are several additions that I'm guessing are Big Sur related.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-16-2021 02:15 PM
Bridge versions are identical between my successful machine and the failing one. iBridge: 18.16.14346.0.0,0
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-16-2021 04:51 PM
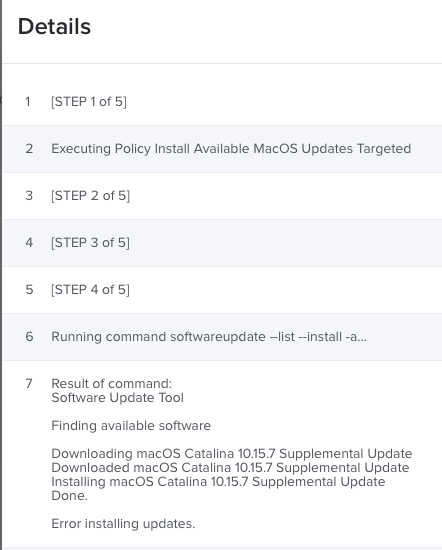
This is getting weirder...
Command Line update fails on both Jamf and Manual with the following error. This is while not on VPN and I had removed our public proxy just to be sure.
Then I used the system preference update and it went through fine. Unfortunately my users will not be able to do that.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-16-2021 05:29 PM
@tomt Same here. Getting tons of errors deploying system updates with downloaded packages and/or by pushing simple, correct "softwareupdate" command - and manual software updates by System Preferences are executing properly
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-16-2021 05:56 PM
@mhasman Well, at least I'm not crazy. :)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-22-2021 07:23 PM
Has anyone found a solid way of deploying this update? I need to get all my systems on 19H524 but the softwareupdate commands are failing.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-23-2021 01:13 PM
I just downloaded the installer via the link above, and installed the .pkg via ARD with no issues.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-23-2021 01:20 PM
@unclemac What build were you on before the update?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-23-2021 04:16 PM
Some were 19H2, and some were 19H15. All updated with the Install function in ARD pushing out the pkg.
Now reporting 19H524.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-23-2021 04:35 PM
Thanks @unclemac, it gives me something to look at. Of course our security blocks the install function of ARD (I'm lucky to have remote control capabilities at all), but this gives me something to go on.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-23-2021 05:21 PM
I put that pkg attached to the police for Macs with 10.5.7 but not 19H524. Still getting "failed" during the installation with Self Service. Not all, but some. Never happened before with Apple's combo updates. IMO means Software Updates provides something else
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-23-2021 06:16 PM
@mhasman I think that's the issue with using the package, it is NOT a combo installer. So I'm guessing that there is something missing that it is looking for.
I just wiped my test machine, reinstalled Catalina 19H1 I think, then I ran softwareupdate --install -a --restart and it fully updated to H524. This had failed before, but, it was with our WSS proxy in place. I also ran across a post referencing tbsc.apple.com as something new in the MacOS update pipeline.
So now I'm going to wipe and start again with everything except the WSS in place. I really hope this gets me somewhere.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 02-25-2021 07:34 PM
Hi, @gabester,
I saw this portion of your post and decided to give it a try. It gave me some hope for getting these machines updated.
Oh, to end on a useful note, in my correspondence with Apple where I was complaining about the lack of standalone downloads from the support site, I was advised that, for limited testing on isolated systems that couldn't run software update, one could always download the associated assets from the same catalog ID along with the .dist file, and with them all in the same folder, run: /usr/sbin/installer -target / -pkg /path/to/folder/with/pkgs.dist I had no idea you could do that with the .dist files, I always wondered what purpose they served! Mind you this is for TESTING and specifically NOT RECOMMENDED for deployment to your fleet... but it's another tool in my belt.
However, when trying it, it seemed to start correctly but then threw an error "The package is attempting to install content to the system volume.". So much for my hopes.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-27-2021 08:38 AM
Hello,
Does anybody have the url to download Catalina Security Update 2021-002?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-27-2021 08:49 AM
@mhasman Hot off the presses: https://support.apple.com/kb/DL2072?locale=en_US
And if you need Mojave: https://support.apple.com/kb/DL2073?locale=en_US
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-27-2021 08:57 AM
@sdagley Thank you, Steve!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 04-28-2021 10:17 AM
I do not miss this struggle, having finally implemented a caching server setup, just using the native softwareupdate command line and/or the jamf software update method has made my life easier. No doubt in the next week I'll run into some edge case that necessitates my revisiting this unpleasantness.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 05-25-2021 11:59 AM
Hello! Does anyone have Security Update 2021-003 (Catalina) download URL, please?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 05-25-2021 12:11 PM
@mhasman Apple finally released the standalone Catalina Security Update 2021-003 .pkg installer on 2021-06-02. Here is the link for the KB article with the download link: https://support.apple.com/kb/DL2075?viewlocale=en_US&locale=en_US
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 06-01-2021 07:28 AM
Hello! Does anyone have Security Update 2021-004 (Mojave) download URL, please?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 06-01-2021 08:22 AM
@Mhomar Apple finally released the standalone Mojave Security Update 2021-004 .pkg installer on 2021-06-02. Here is the link for the KB article with the download link: https://support.apple.com/kb/DL2074?viewlocale=en_US&locale=en_US
Unfortunately there is currently nothing at that link as Apple appears to have forgotten that they have customers that do actually need standalone .pkg installers for security updates.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 06-02-2021 11:07 AM
Thank you so much!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 06-02-2021 11:12 AM
@sdagley Thank you!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Posted on 07-21-2021 06:03 PM
Please share Security Update 2021-004 for Catalina download URL. Thanks!